Centralization is bad for everyone everywhere.
That bring said… I just moved my homeserver to another city… and I plugged in the power, then I plugged in the ethernet, and that was the whole shebang.
Tunnels made it very easy. No port forwarding no dns configuration no firewall fiddling no nothing.
Why do they have to make it so so easy…
The trouble with cloudflare is that there is just one. It’s one of the best registrars out there, the only free/cheap and usable DNS host (have you seen what route53 charges per zone??). That without getting into the whole tunnels and DDoS mitigation end of things, which is nearly unique at any price point.
The problem with cloudflare is that we’re missing three other cloudflares to move to if they decide to pull evil shit.
The bigger trouble is creating a CDN has a stupidly high barrier to entry. You literally need your own data centers across the world, your own server infrastructure, the man power to manage it, etc.
You could try to host it on a cloud provider but you’d go bankrupt even quicker. Unless someone were to try to build a co-op run CDN, it’s just not gonna happen without a profit motive and a large amount of capital.
That’s true. The bizarre paradox of the centralization of edge infrastructure is real.
That said, the other edge-lords (haha) could offer similar functionality, but they chose not to.
I once realized so many of my favourite businesses were cooperatives. I started thinking of what other co-ops I could start and grow. The excitement faded once I realized it would have to not be about the money.
Coops are still about the money. They’re about saving money by sharing resources with fellow workers/consumers, and maintaining democratic control over the company. You’re not going to get rich from a coop (without embezzlement), but you and your coowners will be cutting out the middle man. Obviously, it only makes sense for industries that you’re heavily invested in.
Car making without the tracking bullshit!
I feel like something like https://www.storj.io/ is on the path to what we would want/need?
There might be some additional requirements for a true CDN to ensure data is closer to where it’s needed and in as many regions as needed though with the right amount of bandwidth. The data gets stored all over the place, but that doesn’t mean its optimal. But they do seem to claim it’s faster on their website…
Edit: For those not wanting to click, TLDR is they use excess storage around the world and make it accessible anywhere, and safe from failures. People with excess storage can join the network if they have enough storage/bandwidth and pass some tests. Their API is S3 compatible.
I mean the optimal cdn is maximally distributed to reduce load and latency right. Unfortunatly the web was not built in a manner that supports this.
Eg if we could have a single url for the same object that could be served by any server that is part of the fediverse then the fediverse itself would be an optimal cdn.
Perhaps we should take some notes from peertube. Plus more legitimate bit torrent content on the internet as a whole is hardly a bad thing make the isp’s jobs harder for places without net neutrality.
Look up Anycast when you get a chance.
I consulted with professor gpt and it seams that it’s basicly just giving the same ip address to multiple servers meaning that any of said servers can serve as that ip.
Also it seems said ips require paying large sums of money to isps. My poiny was more that with the current mainstream internet (http websockets etc) it would require you to run a local service/proxy that can interpret a global id and route to basicly any small server with said resource. Unfortunatly i dont think its possible to build such a thing that would just work across browsers if embedded into a standard webpage.
It’s not the only free DNS service.
It’s only a good registrar if you don’t care about privacy and you’re ok with their selection of TLDs (selected only from registries without privacy).
The free accounts do not benefit from DDoS protection. Re-read their terms of service, they’re vague on purpose. If you were ever DDoS’ed (I don’t know who would bother btw but that’s another discussion) they’d just drop you.
You can establish the tunneling thing on your own with any VPS.
The problem with cloudflare is that we’re missing three other cloudflares to move to if they decide to pull evil shit.
You can and should diversify your services and spread them to different providers that are easy to switch. I’ve been with “all in one” providers before, they inevitably end up leveraging their convenience into all sorts of crap. But until you get burned a couple of times they look really good.
It’s not the only free DNS service.
can i get some alternatives. currently basically using cf pretty much just for dns, but would really like to switch
that looks great, thanks o/
EDIT: looks like you can only manage 1 domain before having to contact their support

As it is run by volunteers, they probably want to keep corporate (or domain hoarders) off their platform unless they pay.
makes sense, they support plenty of donation options, if that’s suggested/a requirement to let me transfer in more than 1 :)
Contact support and tell them how many you need and they’ll try to accommodate you. There were a lot of people abusing the service and hosting hundreds of domains so now they’re making everybody request them explicitly unfortunately. They’ve also had to suspend their .dedyn.io DDNS service indefinitely because of the abuse.
That’s why we can’t have nice things.
Please read up on DNSSEC because you will be required to turn it on for every domain you host with them.
I’m not seeing bunny.net on that list, it has a DNS service with API. They have a minimum account maintenance fee of $1/mo and when you load up your account you have to load a minimum of $10. So basically it’s $1/mo for which you get a lot of DNS and CDN service included (20M DNS queries and 100GB transfer).
deleted by creator
only free/cheap and usable DNS host
Check out desec.io als an alternative
That sure does seem to tick a lot of boxes. I’m going to check it out!
I’ve moved a couple of domains to dnssec and it’s great, simple DNS.
there is just one
Well it’s cloudflare, not cloudsflare. Maybe overcasthosting, or sunblockservers…
deleted by creator
So I need to make a VPS setup script to install bind for DNS and wireguard or openvpn and push it to gitlab/GitHub?
I am not sure what that would accomplish.
I have all that, but I still use cf for a ton of stuff.
Why does Cloudflare get a pass on the “if it’s free, you’re the product” mantra of the self-hosting community? Honest question. They seem to provide a lot for free, so…
It’s usually free tiers of paid products
That makes sense, except Google kinda does the same thing. Everything they have is technically just a “free tier” of the Google One subscription, right? I guess I’m saying that “free tier of paid product” doesn’t automatically qualify a company as trustworthy for me. Is there something else that sets Cloudflare apart?
For me personally, it was all about balance.
15 years ago, Gmail/Inbox was a great email client, the domain was great and popular (so no need to spell it out for people) and I would “pay” by getting ads based on my emails read by a bot.
Now Gmail is a terrible email client, the best updates are ridiculous things like moving buttons around and it takes Google years to roll out. The thing loses emails, mislabels and misclassifies stuff and the rules work for a week then blow up. On top of that, google is now basically a proctologist considering how far up my ass they want to go
The balance is broken… Google now officially sucks (IMO)
In my opinion, the difference with Google is that Google is actively using your data and you’re giving them a lot of it. For Cloudflare, what do they have exactly? Depends on what services you use, but really all they get from me is the list of servers that connect to my domains. Google does that too if you use 8.8.8.8, or if you have any of their hardware that overrides router DNS settings like Chromecast and Google TV.
Quality of their products maybe? Cloudflare feels like they put a lot of effort into their product, Google not so much with how buggy everything is and how often they just abandon products they offer.
Google is an advertising company first, everything else second. Of course they shouldn’t be trusted, it’s safe to assume they’ll log and analyze the smallest piece of data
Well search and maps (and some others) have no paid tier. Even for paid products, google does quite explicitly make money from the free version through ads. And most google ads are through third party sites, so you can’t opt out of them by paying google.
Strictly speaking, they’re leveraging free users to increase the number of domains they have under their DNS service. This gives them a larger end-user reach, as it in turn makes ISPs hit their DNS servers more frequently. The increased usage better positions them to lead peering agreement discussions with ISPs. More peering agreements leads to overall cheaper bandwidth for their CDN and faster responses, which they can use as a selling point for their enterprise clients. The benefits are pretty universal, so is actually a good thing for everyone all around… that is unless you’re trying to become a competitor and get your own peering agreement setup, as it’d be quite a bit harder for you to acquire customers at the same scale/pace.
They have for public benefit program where they give out their paid security tiers for free? If you can get recommended into it. Build a lot of goodwill there for non-profits community.
Because most self hosted things are free already. It doesn’t apply to FOSS.
Do you have an alternative to cloudflare tunnels? I’d love to hear it, because I’m also not really happy about relying on them either, but tailscale only works up to an extent because not all devices can connect to it and it’s a pain in the ass to get random family members to connect to it as well.
randomly came across these, so yeah.
edit: about this apparently https://archiveofourown.org/works/54711364
@shiftymccool @Kuvwert cause nobody wants to think about that.
we should definitively have a wiki (though people should use “search” too, I wonder if a wiki would help really). This “topic” comes every month. I have posted this already, here it goes again: https://github.com/anderspitman/awesome-tunneling
That’s awesome thanks!
Thanks for sharing!
Sure it’s easy to set up, but the same behaviour is what I get with my handrolled solution. I rent a cheap VPS with a fixed IP solely for forwarding all traffic through wireguard. My DNS entries all point to the VPS and my servers connect to the VPS to be reachable. It is absolutely network agnostic and does not require any port shenanigans on the local network nor does it require a fixed IP for the internet connection of my home server.
Data security wise the HTTPS terminates on my own hardware (homeserver with reverse proxy) and the wireguard connection is additionally encrypted. There are no secrets or certificates on the rented VPS beyond the bare minimum for the wireguard tunnel and my public key for SSH access.
Shuttling the packets on the VPS (inet to wireguard) is done by socat because I haven’t had the will or need to get in the weeds with nftables/iptables. I am just happy that it works reliably and am happy to loose some potential bandwidth to the kernelspace/userspace hoops.
That’s a good setup.
Does this cause all traffic at the reverse proxy to appear to come from the source IP of your VPS or does it preserve the original source IP?
I’ve been working on setting up a similar setup myself and am trying to figure out specifically how to handle the forwarding on the VPS.
I also have a similar setup to maiskanzler. But I use iptables to forward the traffic over wireguard and I am able to preserve the original client IP by not snat the packets. I then have to use policy based routing to make sure that traffick goes back out through the wg tunnel.
I’m happy to share info on how to get this working.
I’d like a blog please
I’d certainly be interested in full details. This sounds like the best of all worlds of not needing to double reverse proxy, not hardcoding internal IPs in the config of a single reverse proxy on the VPS, and not losing the source IP.
Please tell ^^
I’m not sure what the best way to share this info is. I’d love to write up a blog but not sure how long that would take. I suppose I could just share the wireguard configs here as they include the iptable commands. Will do that tonight when I get a chance.
I have a similar setup and I just have the reverse proxy on the VPS. It then proxies back to the home server on whatever port the service is on. And yes you can forward the original client IP if you wish.
It depends on how you set it up
Yes, I do loose the origin IP and I’m a little bugged by it. It also means that ALL traffic incoming on a specific port of that VPS can only go to exactly ONE private wireguard peer. You could avoid both of these issues by having the reverse proxy on the VPS (which is why cloudflare works the way it does), but I prefer my https endpoint to be on my own trusted hardware. That’s totally my personal preference though.
I trust my VPS provider to not be interested enough in my data to setup special surveillance tooling for each and every possible software combination their customers might have. Cloudflare on the other hand only has their own software stack to monitor and all customers must adhere to it. It’s by design much easier for them to do statistics or snooping.
It also means that ALL traffic incoming on a specific port of that VPS can only go to exactly ONE private wireguard peer. You could avoid both of these issues by having the reverse proxy on the VPS (which is why cloudflare works the way it does), but I prefer my https endpoint to be on my own trusted hardware.
For TLS-based protocols like HTTPS you can run a reverse proxy on the VPS that only looks at the SNI (server name indication) which does not require the private key to be present on the VPS. That way you can run all your HTTPS endpoints on the same port without issue even if the backend server depends on the host name.
This StackOverflow thread shows how to set that up for a few different reverse proxies.
Nice, thank you!
You can do reverse proxy on the VPS and use SNI routing (because the requested domain is in clear text over HTTPS), then use Proxy Protocol to attach the real source IP to the TCP packets.
This way, you don’t have to terminate HTTPS on the VPS, and you can load balance between a couple wireguard peers so you have redundancy (or direct them to different reverse proxies or whatever).
On your home servers, you will need an additional frontend(s) that accepts Proxy Protocol from the VPS (as Proxy Protocol packets aren’t standard HTTP/S packets, so standard HTTPS reverse proxies will drop them as unknown/broken/etc).
This way, your home reverse proxy knows the original IP and can attach it to the decrypted http requests as x-forward-for. Or you can do ACLs based on original client IP. Or whatever.I haven’t found a way to get a firewall that pays attention to Proxy Protocol TCP headers, but I haven’t found that to really be an issue. I don’t really have a use case
Oh neat! That looks like a perfect fit for me! I saved your post and will come back to it once the biyearly “just f*ing fo it again” motivation hits me once more :D
Enough people have already commented on the “proxy at the vps solution”. Another option is to configure routing and nat on the VPS and have it route over the wg tunnel.
Requires you to have postup/predown scripts that modify your routing tables on the wg endpoint.
What VPS do you use for this?
I am using the smallest tier VPS from IONOS for 1€/month. Good, reliable and trustworthy as it is a subsidiary of 1&1 telecommunications.
If you want something cheap check out RackNerd yearly deals. Last I checked they still have listings for black Friday and other old deals once you’ve made an account. I got a server for like $12 a year with 5tb monthly bandwidth. I have 3 servers total with them and haven’t had a problem for the 3 years I’ve been using them.
That would be awesome, currently it’s 500GB for their cheaper option which starts at 23/year. I didn’t find an option to increase the bandwidth before completing the order. Also it needs to be deployed in NY (which would be possibly slow for me in Europe). Finally their isos are somewhat old, the latest Ubuntu they have is 20.04 (which has an EoL next year).
All that being said, 23/year is very cheap for a VPS, and for people in the US that use less than 500GB/month that’s the best deal I’ve ever seen.
There should be more deals when you click add services.

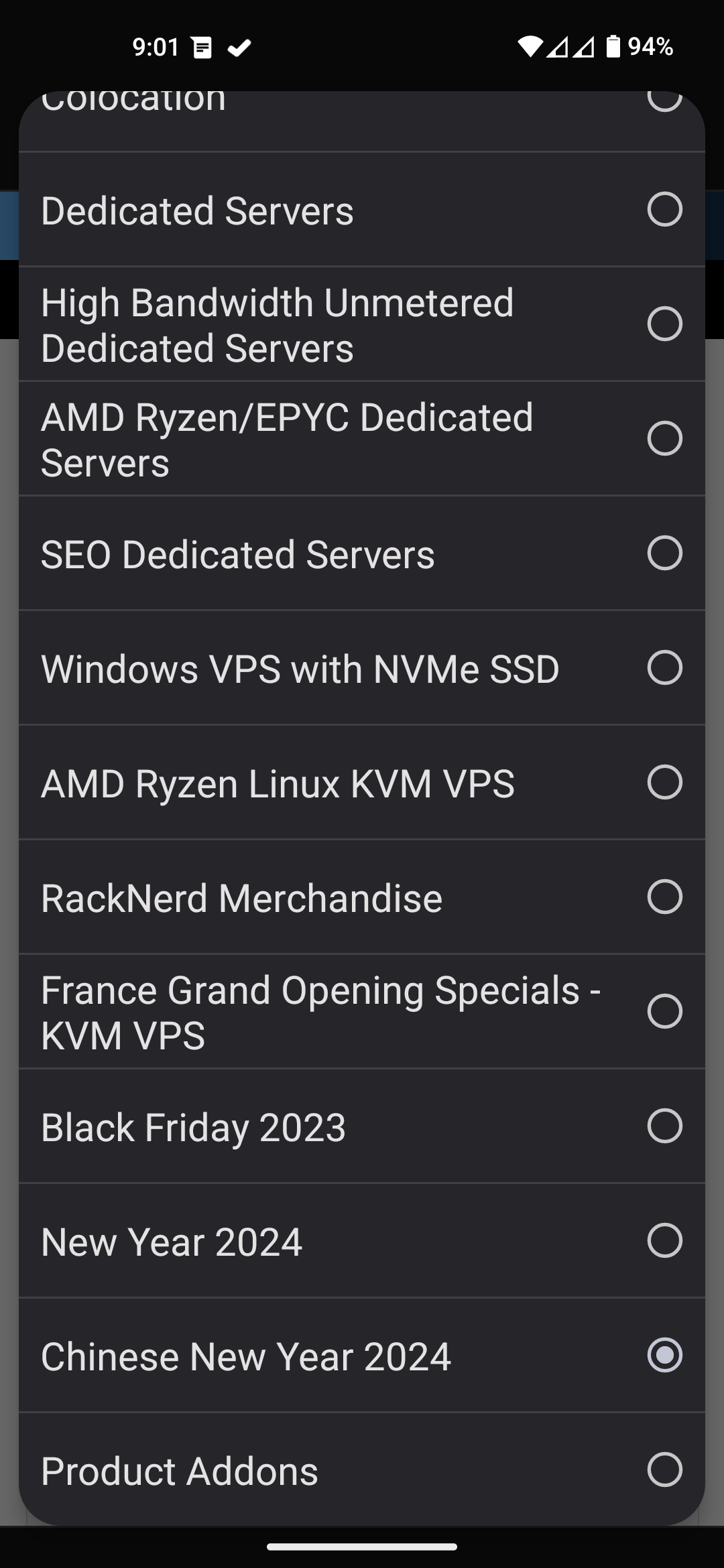
Understand on the latency possibly being an issue. I did see they have servers in France now. Maybe you could do some ping tests.
Thanks, I’m checking that out, but can’t find any “add services” button. Alsp someone mentioned IONOS, which is local to me and doesn’t seem to have bandwidth limits… I was trying to find the poop and they require lots of personal info just to get the account setup, still a bit torn there.
This is the right answer
Same here. Works great, incredibly cheap too.
Acronyms, initialisms, abbreviations, contractions, and other phrases which expand to something larger, that I’ve seen in this thread:
Fewer Letters More Letters CF CloudFlare CGNAT Carrier-Grade NAT DNS Domain Name Service/System HTTP Hypertext Transfer Protocol, the Web HTTPS HTTP over SSL IP Internet Protocol NAT Network Address Translation SSH Secure Shell for remote terminal access SSL Secure Sockets Layer, for transparent encryption SSO Single Sign-On TCP Transmission Control Protocol, most often over IP TLS Transport Layer Security, supersedes SSL VPN Virtual Private Network VPS Virtual Private Server (opposed to shared hosting)
13 acronyms in this thread; the most compressed thread commented on today has 8 acronyms.
[Thread #830 for this sub, first seen 26th Jun 2024, 04:45] [FAQ] [Full list] [Contact] [Source code]
Good bot.
It’s almost like the big tech companies are really good at their jobs…
Woah, let’s not be hasty. A few big tech companies are really good at their jobs…
Let’s not forget the dozens of big tech companies run by absolute morons that bring products that nobody wants or needs and only stay afloat due to legacy, stealing data & selling it, and/or venture capital.
Let’s not forget the dozens of big tech companies run by absolute morons that bring products that nobody wants or needs and only stay afloat due to legacy, stealing data & selling it, and/or venture capital.
You just described Twitter/X
👌👍
Unless you are behind CGNAT; you would have had the same plug+play experience by using your own router instead of the ISP supplied one, and using DDNS.
At least, I did.
Yes, but it does expose your own IP address and thus where you live. Tunnels don’t.
True, but the downside of cloudflare is that they are a reverse proxy and can see all your https traffic unencrypted.
Yes, but if you host a public site it might be a better option, the content is public anyway, and you won’t get doxed if you publish something controversial. It’s a trade-off, between keeping traffic private or keeping your IP private. Wireguard works best for private traffic, but you can’t host a public site with that.
Wireguard works best for private traffic, but you can’t host a public site with that.
Of course you can! Nginx and wireguard on a VPS and actual services wherever you want.
deleted by creator
Your IP changes all the time, it doesn’t matter. The best someone can deduct from your IP is the country.
This is false. Some ISP’s change IP’s often, but some don’t and sometimes geoip lookups can be really accurate. My IP has remained the same since I moved in, and a geoip lookup results in a coordinate less than a kilometer away. It does matter.
I guess you live in a country with loads of spare IP addresses. Here in the UK they change every few days and IPs get rotated between all ISPs, so you can’t even deduct which ISP I’m using. And sometimes my IP is not even a mainland UK IP, but some weird shit from across the world, because Empire, lol.
When looking up my static ip, the location I get is the one of my ISP, not my address. Do you happen to live nearby some central infrastructure of your ISP? (If it seems otherwise, I’m not trying to debunk what you said - I’m just asking curious questions!)
Yes, it seems to be a hit or a miss. I don’t think I live near any central infrastructure or ISP, especially not this specific part of the city.
@qaz @Darkassassin07 what are you even saying? Ip address doesn’t expose where you live. And better get off the internet right now if your concern is exposing your ip cause it was never secret to begin with.
Tunnels stop you from opening a port so nothing is exposed openly to the internet but it does not keep your ip private.Ip address doesn’t expose where you live.
https://letmegooglethat.com/?q=geoip+lookup
Tunnels stop you from opening a port so nothing is exposed openly to the internet1 but it does not keep your ip private2.
This is also incorrect.
- The entire purpose of CF tunnels is to expose sites on the internet
- CF tunnels (and services like it e.g. ngrok) rely on shared proxy servers that forward traffic based on HTTP host headers (which is why you can’t forward arbitrary TCP traffic). The IP of the site will therefore have the shared IP of the company’s proxy server instead of your own.
How do you imagine that geoblocking content works if IP addresses don’t expose where you live?
And better get off the internet right now if your concern is exposing your ip cause it was never secret to begin with.
qaz could be using any of dozens of different methods to obfuscate their IP from the wider internet to write their comment, Tor or a VPN to name just a couple.
No. You are skipping DNS.
I didn’t skip it, I installed ddclient.
Cloudflare is the devil!
and using DDNS
As in, running software to update your DNS records automatically based on your current system IP. Great for dynamic IPs, or just moving location.
Not entirely. CF can protect you from DDOS of up to a few millions of calls per minute. Your home router would melt with that traffic. They also act as a firewall if you enable the proxy dns feature. They do a sanity check before forwarding the call. Also a home router cannot do this. And there’s more.
Both your ISP and CF will drop you like a hot potato if you’re ever under that kind of attack.
CF has other features that are nice like, like WAF, bot detection, geo blocking, caching etc. But it’s only a taste.
All their real services are paid and the whole reason they offer a free tier is to upsell you to their paid services.
@lemmyvore @f2sfljLhdtTZ You can geoock without CloudFlare.
@lemmyvore @f2sfljLhdtTZ cloud flare doesn’t drop you in that situation, I’ve been using them for years and seen them quietly and contently mitigate attacks for my clients
@f2sfljLhdtTZ @Darkassassin07 Eveyone so worried about DDoS. They are not going to DDoS a resedential Ip address. Sure if youbpiss someone off they well they’re going to do it even without selfhosting anything.
I can assure you that before I set up Cloudflare, I was getting hit by SYN floods filling up the entire bandwidth of my home DSL2 connection multiple times a week.
Sure, cloudflare provides other security benefits; but that’s not what OP was talking about. They just wanted/liked the plug+play aspect, which doesn’t need cloudflare.
Those ‘benefits’ are also really not necessary for the vast majority of self hosters. What are you hosting, from your home, that garners that kind of attention?
The only things I host from home are private services for myself or a very limited group; which, as far as ‘attacks’ goes, just gets the occasional script kiddy looking for exposed endpoints. Nothing that needs mitigation.
I also really like the tunnels feature. It makes self hosting at home easy for those under NAT/CGNAT or whatever it was called.
I prefer Tailscale Funnel for these kinds of things. NetBird and ZeroTier also work just fine if you don’t want to expose your services to the public.
Tailscale is so cool too. I’ll definitely be switching if I can ever use my own domains
Actually you can… I do that with my setup. Just point your domain to the new ip assigned by tailscale to your server. Thats all. Recently they started supporting the https certificate also… Even though it’s not needed, for internal only communication.
You can set A DNS entries without wildcard in the configs (with head scale at least), just use their magic DNS thing that works with hostnames or just self host DNS and tell your tailnet to use that.
I looked at headscale but as far as I can tell their is no active directory or SSO integration. Which is very unfortunate.
Good news, they support OIDC! Haven’t tested it myself so your mileage may vary.
Just stop supporting the biggest actor in the market.
That’s just a bandaid on capitalism’s issues. Urging people not to support the biggest actor will never work in the grand scheme of things, when said actor provides their best immediate interests.
I use Cloudflare as my registrar and public DNS. And only for that. Sorry but they don’t get to peek at my network traffic.
Well, centralization and giving up your freedoms, letting someone else control you, is always kinda easy. Same applies to all the other big tech companies and their platforms. I’d say it applies to other aspects of life, too.
And I’d say it’s not far off from the usual setup. If you had a port forward and DynDns like lots of people have, the Dns would automatically update, you’d need to make sure the port forward is activated if you got a new router, but that’s pretty much it.
But sure. if it’s too inconvenient to put in the 5 minutes of effort it requires to set up port forwarding everytime you move, I also don’t see an alternative to tunneling. Or you’d need to pay for a VPS.
Their static website hosting is probably the best in the business. We seriously need some competition though.
Even when you host a HUGE static website (e.g. maps with thousands of image files). You can just throw it on R2 add a few transform rules, point a domain at it, and you are done. Also highlights the usability of Cloudflare compared to other solutions.
There are tons of CDNs out there.
I mean, I used to think Google Public DNS was great until I switched to 1.1.1.1…
If you like 1.1.1.1 the. You should try 9.9.9.9. Or better yet host unbound pihole if you’re up to the challenge. Best dns experience I’ve had.
If you use 9.9.9.9, you should try Mullvad DNS (with adblocking) or AdGuard Public DNS
Since we’re all throwing out DNS options, I’ll toss in NextDNS
I already use pihole, but with cloudflared as the upstream. What benefits does unbound offer besides improved security?
It’s actually better privacy since it talks directly to the root servers instead of cloudflare knowing all of your DNS traffic. Quad9 is a good alternative with better data policies
So now your ISP sees all of your queries instead of CF. (Assuming the cloudflared option is using DoH)
I’ll trust Cloudflare over Comcast/AT&T/etc. any day of the week.
It looks like Quad9 supports DoH: quad9
Your ISP knows where you’re going anyway. They don’t need DNS for that. They see all the traffic.
You might want to study more about SNI. Your ISP knows anyway
I know plenty account SNI already, but thanks. You might want to study more yourself, since we’re being condescending.
Well, running your own DNS server will also give you eSNI. And Cloudflare still doesn’t know anything
You can run a VPN and tunnel your outbound DNS queries over that. Heck, you could tunnel your DNS queries over TOR
What benefits are you having from switching?
1.1.1.1/cloudflared responds crazy fast compared to anything else i’ve used. I really just wanted off Google (and before them OpenDNS). That’s about it.
Commenting as I am curious about this too!
9.9.9.9
I am out of the loop, what’s going in with snooping?
I use their cloudflared tunnel sometimes for accessing home hosted stuff.
Because Cloudflare acts as a reverse proxy it can see everything that happens in a session.
This is also known as a man in the middle attack. But Cloudflare meds to do this in order to do it’s checks for bad actors.Now, as Cloudflare has access to the unencrypted traffic and we know that NSA is all about data vacuuming due to the Snowdn leaks we can make a tin foil hat guess whaylt goes on.
Just note, OP, that the last part of his statement is pure speculation. The first part is technically true, which can lead to that inference, but no information has been released which corroborates it. However, that does not mean it’s not possible.
This is true. Which is why I said tinfoil hat guess.
Though those leaks showed they actually did it on a large scale. I don’t think they stopped for some arbitrary reason. Why would they? And technology developed further, surveillance is only getting easier. I’d say even without a tin-foil hat on, it’s more likely they do it than not.
@ramble81 @slazer2au sure but they had PRISM to think they are still not doing something like that is absurd. We know they’re doing it and cloudflare would be a perfect target.
I don’t understand why Cloudflare gets bashed so much over this… EVERY CDN out there does exactly the same thing. It’s how CDN’s work. Whether it’s Akamai, AWS, Google Cloud CDN, Fastly, Microsoft Azure CDN, or some other provider, they all do the same thing. In order to operate properly they need access to unencrypted content so that they can determine how to cache it properly and serve it from those caches instead of always going back to your origin server.
My employer uses both Akamai and AWS, and we’re well aware of this fact and what it means.
Thank you!